The popular ad-blocking tool, u-Block Origin has stopped working on TradingView and users are reporting an abundance of ads and upgrade ‘nag screens’. TradingView is a platform used by over 90 million traders (at the time of writing) across the world to chart out price action on many stocks, Forex and cryptocurrencies.

TradingView is not free for many advanced features. There is a capable free version of it though, and for many years, people in the know have used uBlock Origin, a browser plugin, to block the pop-up boxes and ads for TradingView’s paid packages. This ability to bypass nag screens will soon stop working, with Google’s rollout of Manifest V3 to Chrome browser (and other Chromium based browsers). In short, this dramatically affects the ability of extensions like uBlock.
The top investing website?
We feel that TradingView’s rise to the top has doubtless been helped by the fact that there is a free option. SimilarWeb lists it as the top ‘investing’ website, although this could be a misnomer since we believe that it’s primarily a very capable charting tool with some news, community ideas and other stuff sprinkled in. In countries where paying a subscription is really impossible for those starting out, a free version is a lifeline.
Here is how you can currently block those pesky ads:
Use Firefox for TradingView
Firefox is a free browser that focuses on privacy. It also is NOT based on Chromium so doesn’t suffer the same problems in many respects that Chrome, Edge, Opera and quite a few others do (they ARE all based on the Chromium ‘engine’).
A few special features of using uBlock within Firefox are:
- Firefox waits for uBlock origin to be ready before sending network requests from any tabs that are already opened at browser launch time. In other browsers, trackers can be enabled at launch time. This is a big thing, especially when using default-deny mode for 3rd-party resources or JavaScript!
- Pre-fetching (think pre-loading stuff you might not use to give he impression of speed) is blocked in Firefox and not in Chromium-based browsers who just let the website decide what to download for you. Prefetching is disabled, by default, in uBlock Origin.
- The Firefox version of uBlock Origin uses WebAssembly code for core filtering code paths. Chromium-based browsers don’t do this because of permissions in the extension manifest.
So, I suggest two decent methods here:
- Switch to Firefox as your main browser and carry on using TradingView and uBlock Origin.
- (My suggested method) Keep your current browser and just open up Firefox when you want to trade. This works nicely with two screens as well, tracking your stocks, Forex and crypto with great indicators in a clear, uncluttered environment. Most computers can handle two browser windows.
There’s also a lot to be said about separating trade analysis from the main browser you use for work or leisure. Focus will remain on the charts and you shouldn’t get distracted as much.
Paying for the full TradingView package
While I bring these workarounds to your attention, please note that I personally pay annually for TradingView because it gives me the option to run multiple charts and indicators, This is very useful when you have multiple stocks, currencies and cryptos to track and enjoy getting confluence on signals from many indicators. Do consider this if you have the money and feel you get value from the service, TradingView has become a really great resource that deserves funding. Also, perhaps appreciate that if you do a significant amount of trades, the cost of upgrading TradingView could pay for itself… several times over if you do it right.
Either way, happy (uninterrupted) trading and analysis!







 It’s difficult for us to write an unbiased HDD Regenerator review because we use it all of the time in our repair shop. It’s the single best tool out there for repairing corrupt hard drives, and we get lots of them in. That said, we’ll try to remain objective and give an honest review.
It’s difficult for us to write an unbiased HDD Regenerator review because we use it all of the time in our repair shop. It’s the single best tool out there for repairing corrupt hard drives, and we get lots of them in. That said, we’ll try to remain objective and give an honest review.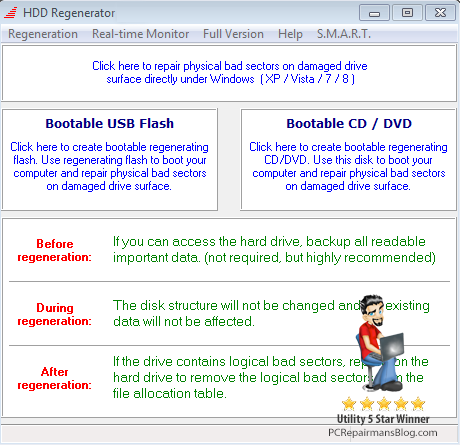
 Since I wrote the original
Since I wrote the original 
 If you need to execute a shell script and can’t get your head around the conflicting information out there, I’ll try to clear things up. There are quite a few ways to execute a shell script and each has its pros and cons. If you are coming from a Windows environment where the file extension dictates how we handle the file, then try not to think like this. A script can have no extension but still be run. So, let’s take a look at our four ways to execute a shell script.
If you need to execute a shell script and can’t get your head around the conflicting information out there, I’ll try to clear things up. There are quite a few ways to execute a shell script and each has its pros and cons. If you are coming from a Windows environment where the file extension dictates how we handle the file, then try not to think like this. A script can have no extension but still be run. So, let’s take a look at our four ways to execute a shell script.